 The recent Equifax hack has millions of people worrying about the security of their personal data. While this was a particularly egregious and dramatic attack, it’s certainly not the only one. And nonprofits are not immune. Which is why I asked an expert for advice as to what nonprofits can do to protect themselves and their donors. Ged Mackey is Chief Technology and Security Officer of MobileCause. He told me about a problem I’d never heard of called “Card Testing.” Here’s what he had to say.
The recent Equifax hack has millions of people worrying about the security of their personal data. While this was a particularly egregious and dramatic attack, it’s certainly not the only one. And nonprofits are not immune. Which is why I asked an expert for advice as to what nonprofits can do to protect themselves and their donors. Ged Mackey is Chief Technology and Security Officer of MobileCause. He told me about a problem I’d never heard of called “Card Testing.” Here’s what he had to say.
Carding Testing is On the Rise
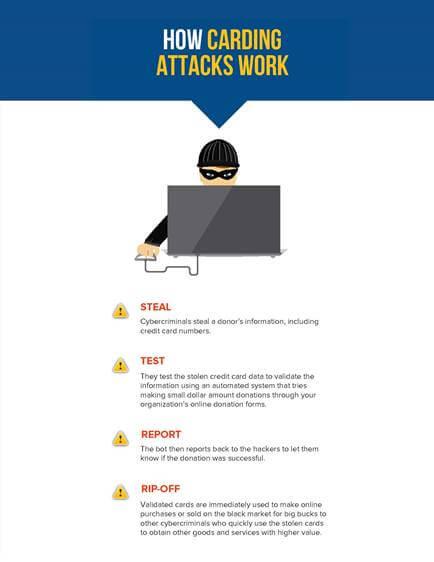
A report by Symantec released earlier this year revealed that nearly half of all U.S. companies experienced two or more cyberattacks, many of which focused on identify theft and typically stolen credit card information. Following such a breach, these cybercriminals will test the stolen credit card numbers by making small online web donations to verify that the card is still active.
This form of crime is called “Card Testing” and is dramatically on the rise — 200% in just 2017 alone (per Radial’s recent report from May of this year). The tactic can be manual or automated and is used by fraudsters to test stolen credit card numbers and check their validity.
The automated approach uses scripted bots to make small donations to a charitable site at a rapid pace, often dozens of donation attempts per minute.
The Present Danger: Nonprofits are Targets
An attack of this nature can look like a DDOS (Denial of service) attack and can cause a shutdown of the network or the payment processor itself. What this means is that your bank will stop accepting donations or payments until the issue is resolved.
Each card that cybercriminals can validate online is worth good money on the black market and is quickly used to obtain other goods and services with a higher value.
This ability to verify small amounts from tens of thousands of different types of cards in many different countries seems to work more reliably with nonprofits than larger entities, because these targets often lack adequate fraud controls. Nonprofits seem particularly susceptible given they often have simple online forms to make it easy to collect donations and, just like buying any kind of digital good, no shipping address is required to complete a purchase.
Unfortunately, this kind of fraud impairs organizations with chargeback fees, lost sales or donations, administrative time and potential to damage their reputation.
How to Protect Your Organization From Carding Attacks
Fraudsters regularly identify the security-weak, cardable websites and brazenly share their names and URLs on pages dedicated to showing other hackers how to pull off the carding fraud.
So, what can a nonprofit do to protect itself?
First, understand where your weaknesses may lie. Factors like manually storing credit card numbers in hard copy or in a computer in clear text or other non-encrypted, human readable accessible form have left organizations vulnerable to cybercriminals costing them significant time and money.
Second, work only with credit card payment processors that uphold the highest security standards. PCI Level 1 DSS is the industry’s highest standard for payment processors and demonstrates they have submitted and passed a rigorous and comprehensive process involving a full-scale audit to validate all areas of a business that encounter credit cardholder data. The PCI standard defines over 300 controls that include everything from corporate security policy to use of latest security hardware, testing of breaches, physical controls and encryption to be used.
Third, the Visa Global Registry of Service Providers is another way that organizations can verify their payment processors of choice. Visa advocates educating your stakeholders about protecting their data and encourages organizations to only use certified payment processors, while also developing a contingency plan in the event of a fraudulent carding attack in the form of:
- Cyber security education: Provide a basic understanding of cyber security and the role your staff and donors play in it. For example, remind donors to monitor their online activities including checking their debit and credit card statements so they can notify you and their banks if any unusual activities show up.
- PCI Level 1 certified payment processor: The best practices are to guarantee the third-party payment processor does not store credit card numbers. A qualified vendor will ensure that once a card is entered onto a form it is immediately tokenized. This means that the number is turned into a form that is not human readable. The unreadable number is still encrypted in transit (as it goes through the internet) and at rest (when it is stored).
- Contingency planning: Have a response plan in place in the event of an attack that includes alerting donors about the breach and providing clear instructions about what they need to do. Be open and transparent about what exactly happened and let them know about any steps you are taking to resolve the issue to minimize the negative impact and prevent further damage.
Some Best Practices
1. Nonprofits should consider requiring a few more fields on their online payment forms to help decrease their chances of carding attacks. At a minimum, the forms should ask the donors for their email, phone, zip and card verification value (CVV). While this could potentially increase the decline rate and flag your payment processor, they are necessary steps to prevent charge backs from fraudulent activity.
2. Nonprofits should enable a reCAPTCHA system. A reCAPTCHA-like system is designed to establish that a computer user is human (protecting websites from bots).
3. Nonprofits should use velocity checks if possible. Velocity checks are a frequency check in which payment transactions are reviewed for repeating patterns within a defined (short) period. The check can be performed based on various data for a payment transaction (e.g., if a certain pattern repeats during a period, or even appears in clusters).
The points above should help with the majority of cases. Should attacks still be of some concern, there are more sophisticated products/approaches on the market that do carry a cost, as well as technical expertise. They mostly rely on using Web Application firewall, device fingerprinting or pattern/risk recognition. These software packages often use elements of machine learning and reference databases of known “bad actors.”
While nonprofit organizations are most vulnerable to carding attacks, they can quickly follow the above-mentioned steps to protect their data management systems against potential cyber threats. For a visual representation of the problem and the fixes, see the infographic below.

 Guest Author
Guest Author
Ged Mackey is Chief Technology and Security Officer of MobileCause. Ged has more than 20 years’ experience in leading software teams and bringing products from inception to market. His expertise spans a wide range of technologies and domains, from enterprise applications to highly complex middleware and security products. A highly skilled security ninja, Ged keeps nonprofit organizations safe from fraudsters with secure donation processing systems and protocols.





EXCELLENT article! Sending it to each of my nonprofit clients NOW. Thank you, Ged Mackey and Ms. Clarification! Margie McCurry
The McCurry Group MARGUERITE MCCURRY, Ph.D., Certified Fund Raising Executive
Public Relations for nonprofits-
‘They won’t give if they don’t know who you are!”
PO Box 2407, Monterey, CA 93942-2407